In light of all the recent news on cyber threats and attacks, we thought it was time to refresh our article on cyber security from last year. Having an adequate understanding of cyber security not only provides individuals with the opportunity to better protect their private information on and off the web, but also allows them to recognize when and/or why they are at risk. Below are a number of recommendations from Condor Capital on how to sufficiently safeguard yourself against potential security vulnerabilities:
Passwords
There are two simple solutions that can help prevent most cyber attacks that result directly from issues involving passwords, with the first being the strength and storage of your passwords and the second being multi-factor authentication.
Installing a password vault/manager to your device will help optimize your overall password strength and variability. Password management applications are used to safely generate and store all of your passwords. Since the purpose of this type of program is to safeguard all sensitive information within it, the vault encrypts all of your passwords. Using a master password that you create, the vault will decrypt all information and either enter it for you or display it to you to enter manually. Overall, this tool provides you with the ability to create strong and unique passwords for all of your critical services, thereby protecting you in the event that one of your passwords is compromised. Condor Capital recommends that you use multifactor authentication with a password vault or not use one at all.
Activating a second-factor authentication method with a service will ensure that you are, in fact, the person accessing the service. There are three different factors of authentication: something you know, have, and are. For example, something you know could be a password, something you have could be a cell phone, and something you are could be a biometric scan. Microsoft is a recent example of a company utilizing multi-factor authentication to improve overall security with its Windows 10 upgrade and building two-factor authentication as a core security feature. Another example, which is becoming increasingly popular among well known companies such as Amazon and Facebook, is the confirmation code text message. When an incorrect password is entered multiple times, by default, a text message gets sent to your phone prompting you to enter the displayed code on the required webpage. When entered, you may continue onto your account with that provider. Another widely used method is a mobile app authentication service such as Google Authenticator. In addition to a user name and password, you will be required to enter the sequence of numbers appearing in the app at the time of login. Condor Capital recommends that you enable multifactor authentication on all services that provide it. You can see a list of services that use two factor authentication at http://twofactorauth.org.
On the Web
Posting personal information to social networks such as Facebook, Twitter, or LinkedIn creates yet another avenue for attackers to gather information on you. When securing yourself in terms of social media and other websites, make sure your network of friends is carefully chosen and you use websites that are HTTPS secured.
When using social media sites, turn your security feature and privacy settings to their strictest level to prevent unauthorized people from viewing your personal information. Subsequently, you should think carefully before adding a new person to your “network.” Most social networks give you the option to change privacy settings, thereby limiting your content to connections of certain groupings. In addition to social media outlets, there are increasing numbers of commerce and general interaction services on the web so it is crucial to ensure that the websites you are using are secure.
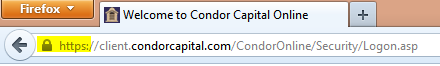
Whenever connecting to a website that collects personal information, facilitates payment, or transfers funds, you should ensure that it is being done over an encrypted connection. An easily identifiable sign that the website is secure is the display of “HTTPS” or a padlock in the URL when connected to the site (see example below).
Technology companies across the country have stressed the importance of HTTPS, regardless of the content of the webpage. This is because HTTPS not only encrypts information, but also authenticates who you are communicating with. Major search engines, such as Google, have adopted HTTPS as an additional criterion that is taken into account when ranking searches. As a result, websites with a secure web address are displayed first. Google is also encouraging companies to fix weaknesses that have come to light in recent months on the SSL protocol, which underpins HTTPS connections, by dropping support for known weak algorithms from their Chrome web browser.
Many individuals have numerous email accounts, whether it be school, personal, or work email. With that said, the more accounts you have, the more at risk your personal information is. With email being such a prominent form of communication, spam, phishing, and the possibility of unsecure transmissions put you at risk across all your accounts.
While most spam is harmless and usually ends up in your trashcan, other forms of spam contain malicious malware and, when clicked, will wreak havoc on your device. In addition, malware can open a door to hackers who are seeking to obtain your personal information or passwords. Setting up a spam filter on your email is the first step towards your protection against this threat. If a filter is already present, you can update your settings to filter incoming emails more scrupulously. Do not open any emails or attachments from unknown senders or from senders that do not display trustworthy characteristics.
One of the most frequent forms of an email based attack is phishing. Phishing occurs when an attacker attempts to acquire personal or financial information by impersonating a trustworthy source, such as your bank or credit card provider. To guard against such schemes, always be cautious when someone contacts you regarding your accounts. It is standard protocol that many organizations will not ask you to provide information, such as account numbers or passwords, in this manner. In addition, always be wary of links within an email prompting you to enter personal information. An effective way to help identify fraudulent emails is to look for any obvious spelling or grammatical errors, which would be unlikely in an official document.
You should always exercise caution when transmitting sensitive information using email. Also, make sure that your email providers support both encrypted connections and encrypted sent/ received messages. This feature has spread out to more ISPs since this article was last released and now includes many more e-mail providers. More information regarding which providers use such technology can be found online.
Mobile
Mobile devices, such as smart phones and tablets, are a prime target for cyber based attacks. The best way to ensure your mobile device does not become a threat to your security is to overcome common misconceptions, use a PIN lock, and download software updates.
A common misconception is that a new device is safer closer to the time of purchase and as time elapses, it becomes unsafe. This is simply not the case, especially because some devices come pre-installed with vulnerable adware. Lenovo was recently put under the spotlight when the Superfish program that comes preloaded on their laptops was found to inadvertently make it easier for hackers to infect systems. Another common misconception is that all app downloads are safe, which is also not true. Always be wary of app downloads from an unknown developer, as these apps can sometimes pull personal information from your device and/or lock your mobile device from your use.
Another way to ensure your eyes are the only ones on your information is using a security PIN to lock your phone. A PIN is enabled through your settings and will require you to make a four digit number or a pattern that will be used to unlock your phone. This is particularly important when the device is used to access email, which likely contains a trove of personal information.
Finally, be sure to keep your operating software as up-to-date as possible. In addition to fixing bugs, many updates patch up security flaws that have been discovered in the code. As annoying or lengthy as the updates may be, they are an effortless way of ridding potential security threats that pertain to your mobile device and other devices as well.
Cloud
Although the cloud is still a mystery to many of us, security problems do exist. Since the cloud gives you access to your data from anywhere, it is highly targetable for an attack. And while cloud systems are constantly monitored, they are also constantly growing in size, increasing their target value. It may be easy for an attacker to hide within all the noise generated from the many legitimate users on a system. A recent example of cloud technology being hacked is attributed to celebrity iCloud accounts being compromised. Stars like Jennifer Lawrence had personal photos leaked onto the internet, showing that anyone can be the target of such an attack.
Condor’s Suggestions
Considering the above, listed below are a few steps Condor Capital proposes to take in order to protect your security:
- Require two-factor authentication
- Utilize email that supports encrypted viewing and transmission
- Shred all documents with sensitive information
- Ensure several layers of hard and soft firewalls to protect systems
- Maintain confidentiality agreements with all vendors
- Verifications sent by phone of requests to withdraw funds
- Work with custodians to verify the authenticity of suspicious emails received
- Purchase cyber security insurance if at large risk